Dashboard example
Uploading an SSH key
The first thing we need to do is to make sure we have a way to access the
instances we create. We use SSH to allow access to our instances. You can
either import an existing public key or have Catalyst Cloud create a key
pair for you. We document both below:
Creating a new key pair
If you haven’t generated a SSH key pair before, Catalyst Cloud can create one
for you.
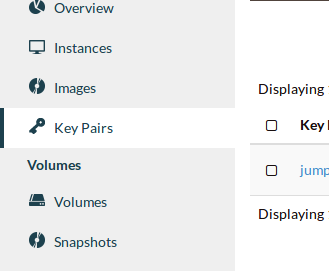
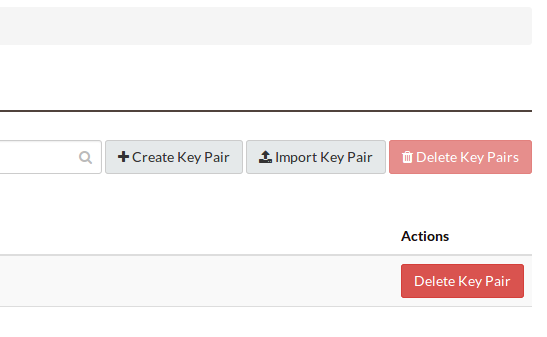
Navigate to the Key Pairs tab.
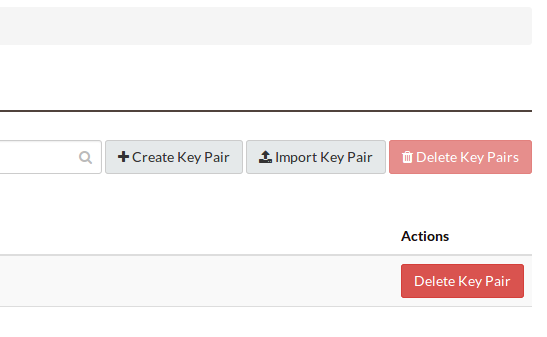
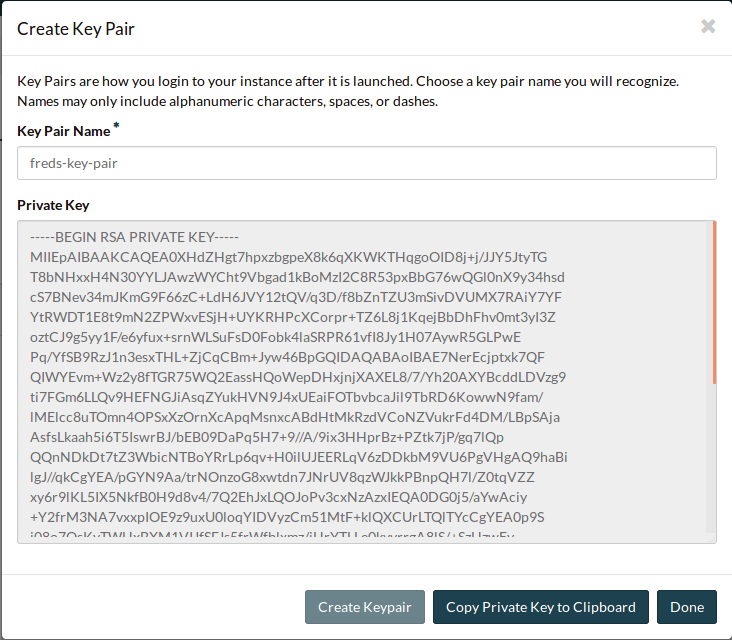
Select the Create Key Pair button.
Name and create the key pair.
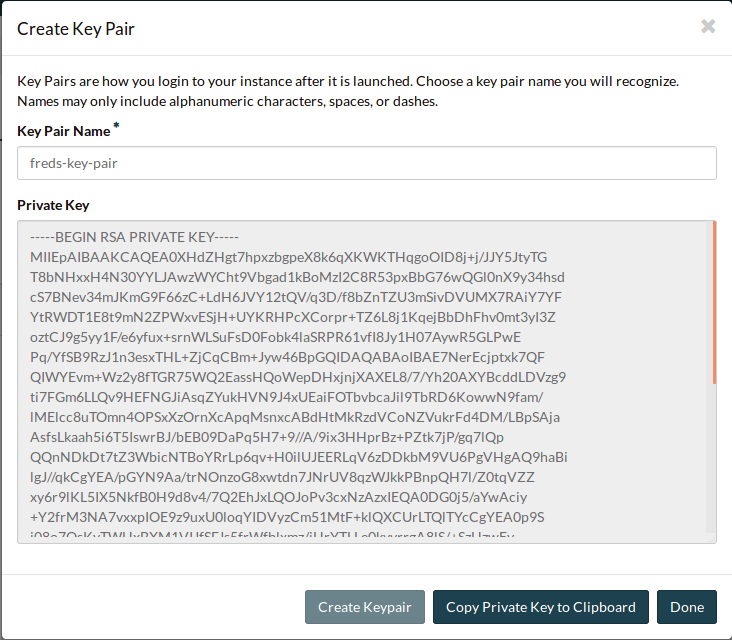
Click Copy Private Key to Clipboard and paste it into a text file in a
secure location. Make sure the file is saved as plain text.
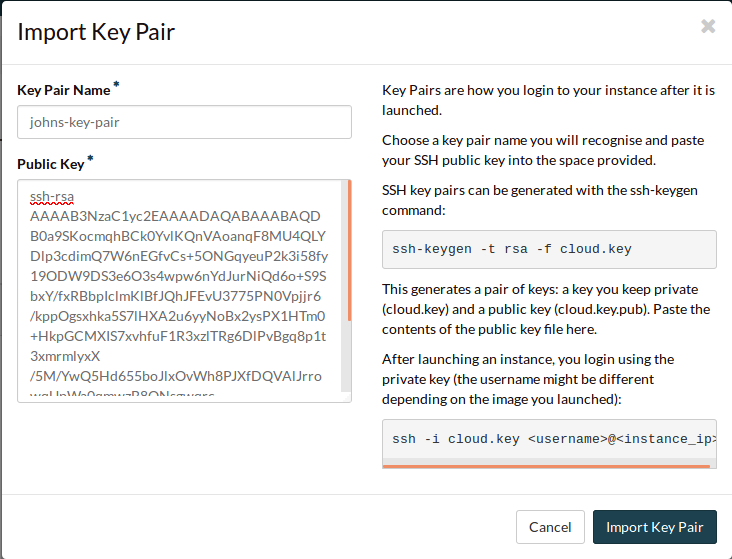
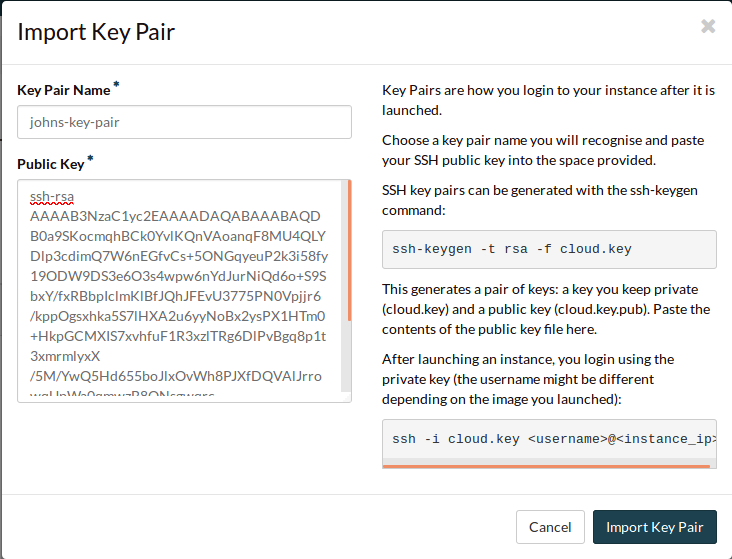
Importing an existing key pair
If you already have an SSH key pair, you can import the public key onto
Catalyst Cloud.
Navigate to the Key Pairs tab.
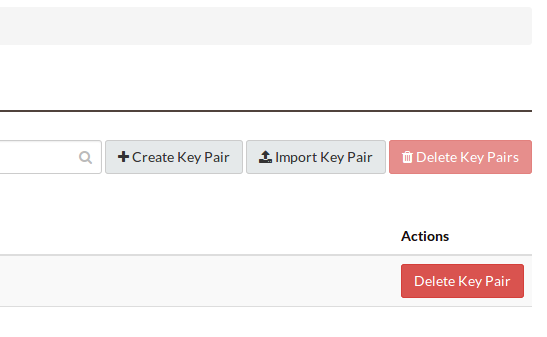
Select the Import Key Pair button.
Name the key pair, and paste your public key into the box.
Now that you’ve either imported or created an SSH key pair, we can continue.
Booting an instance
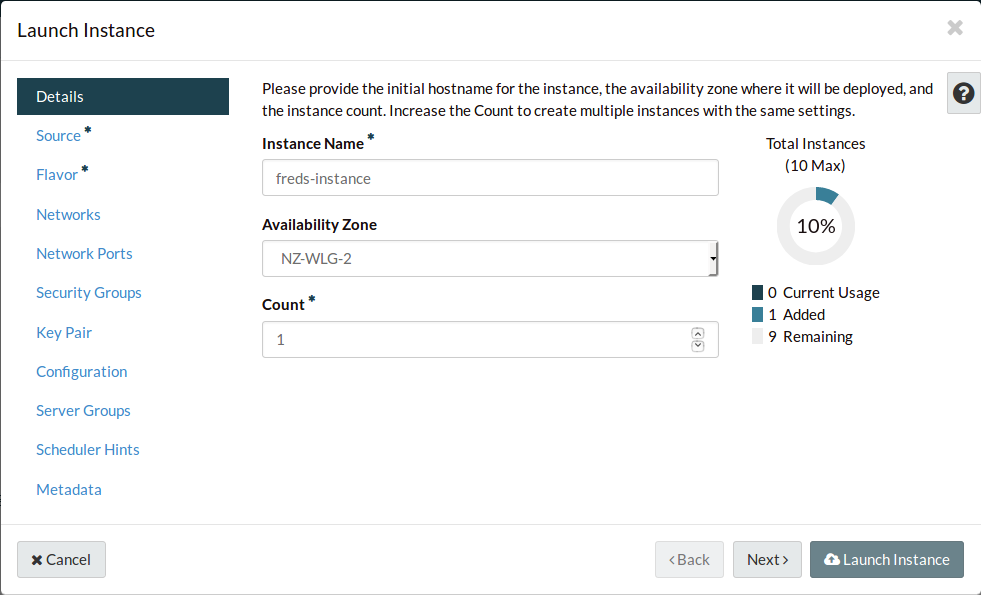
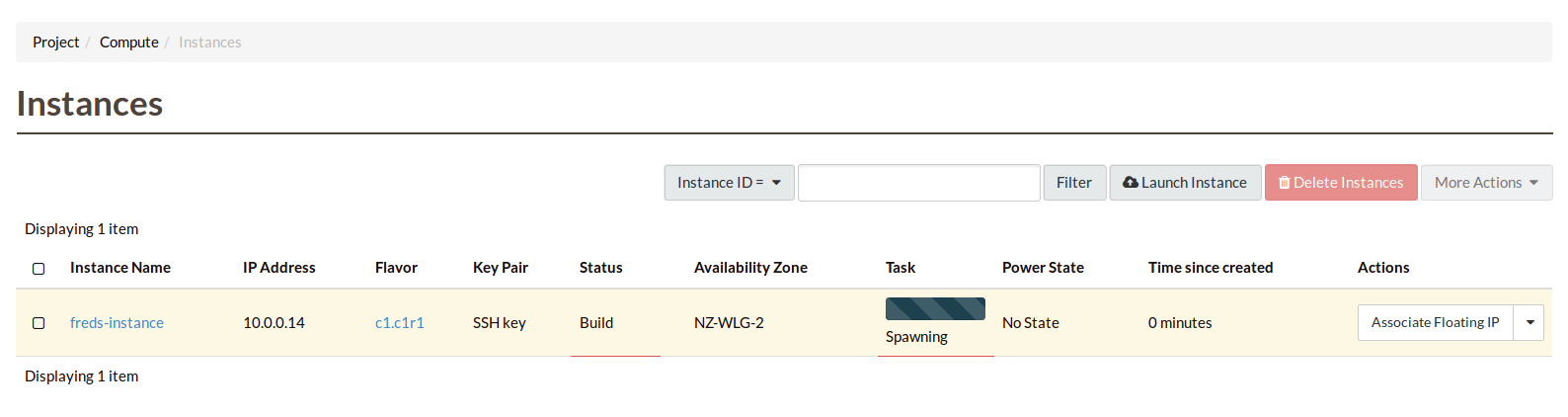
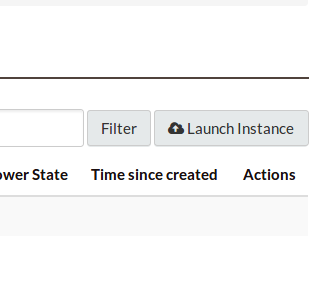
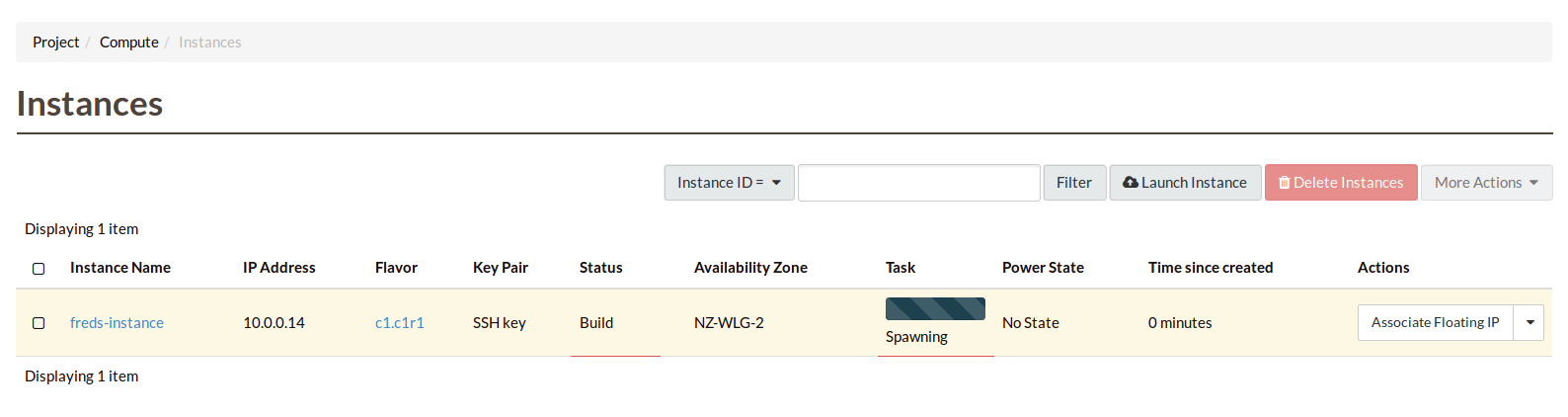
We are now ready to launch our first instance! Navigate to the Instances
page.
Select launch instance.
Name your instance.
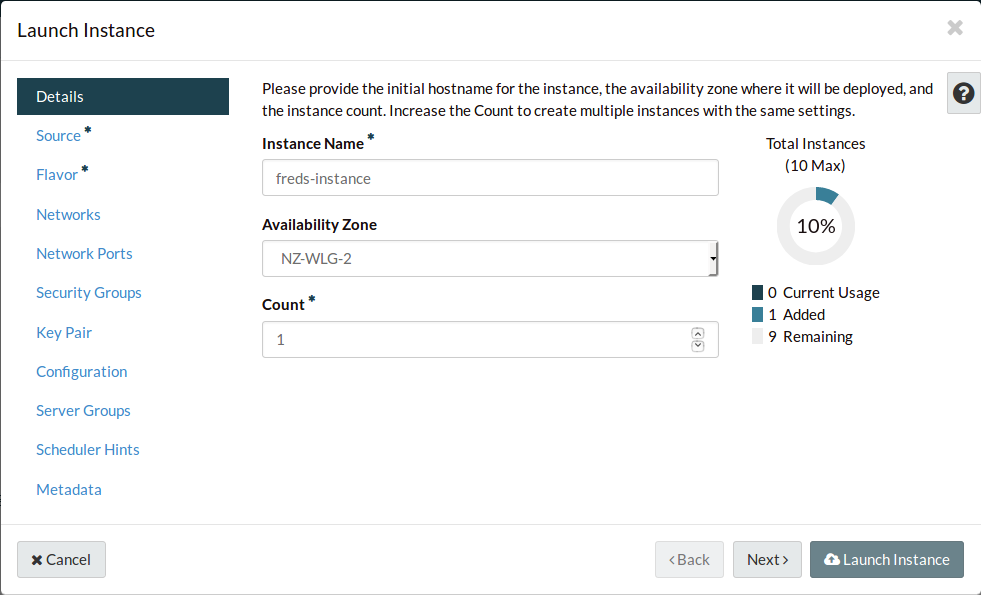
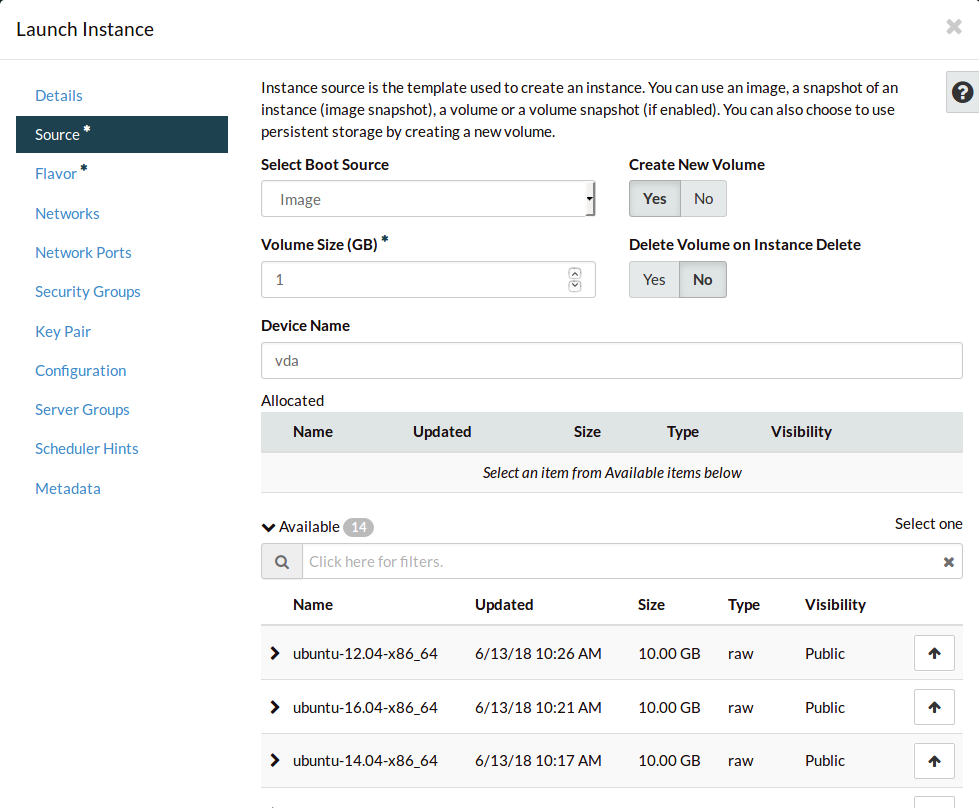
Navigate to the Source tab.
There are many types of sources you can use for your instance. In this case,
we’ll use an Image to create a standard Ubuntu installation.
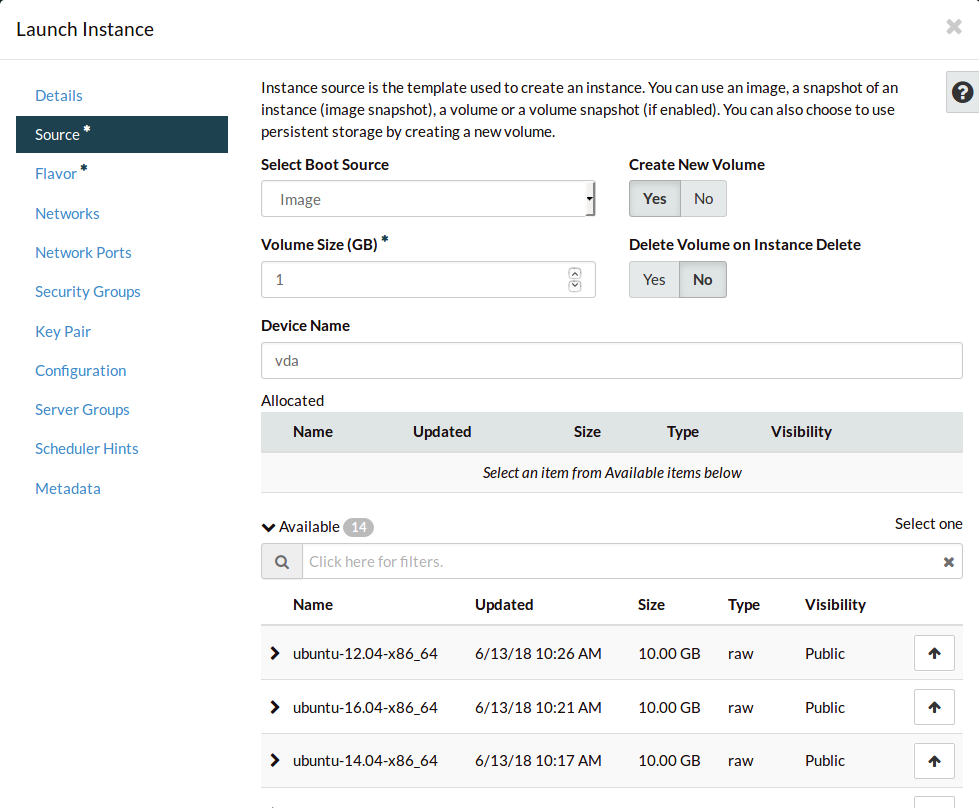
Search for Ubuntu.
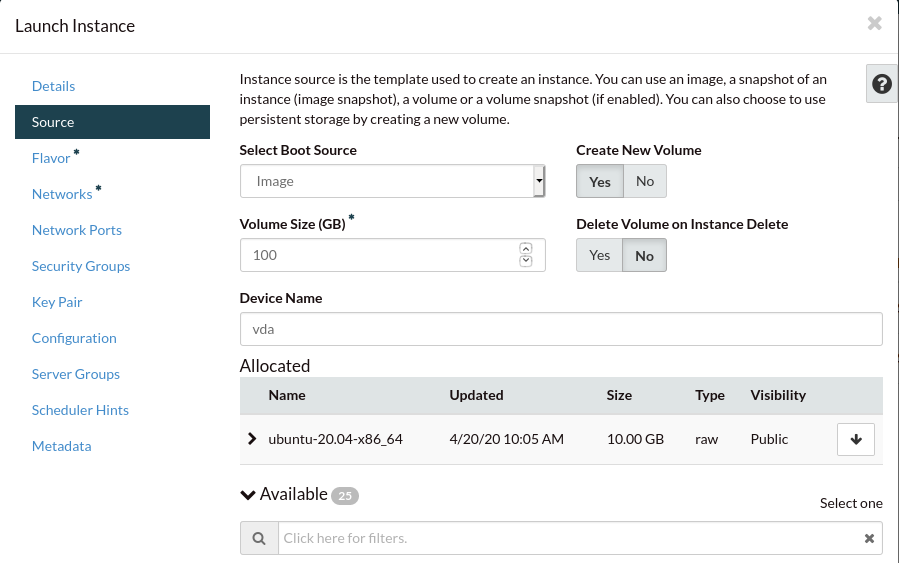
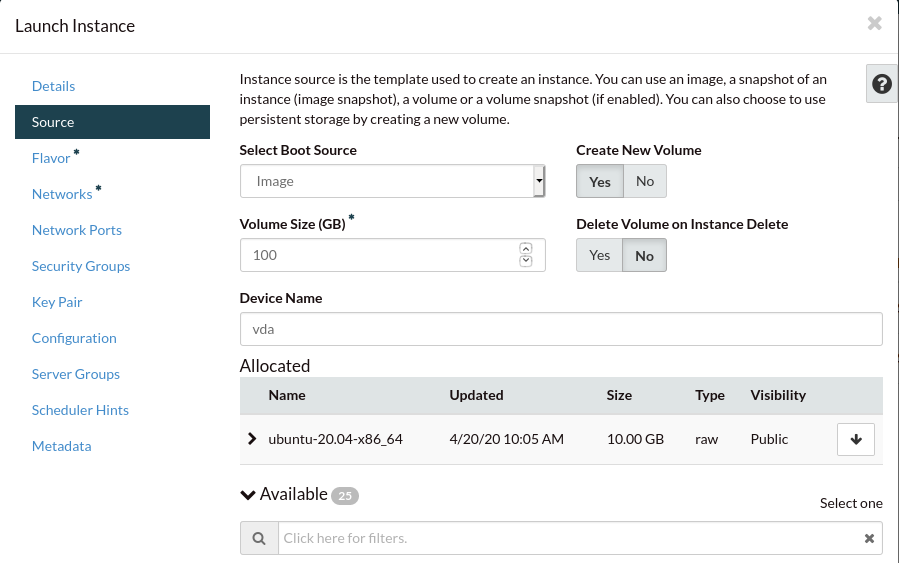
Select the image for Ubuntu 20.
By default the volume will just be large enough to hold the image’s files.
We’ll increase it to 100GB so we have enough space for later.
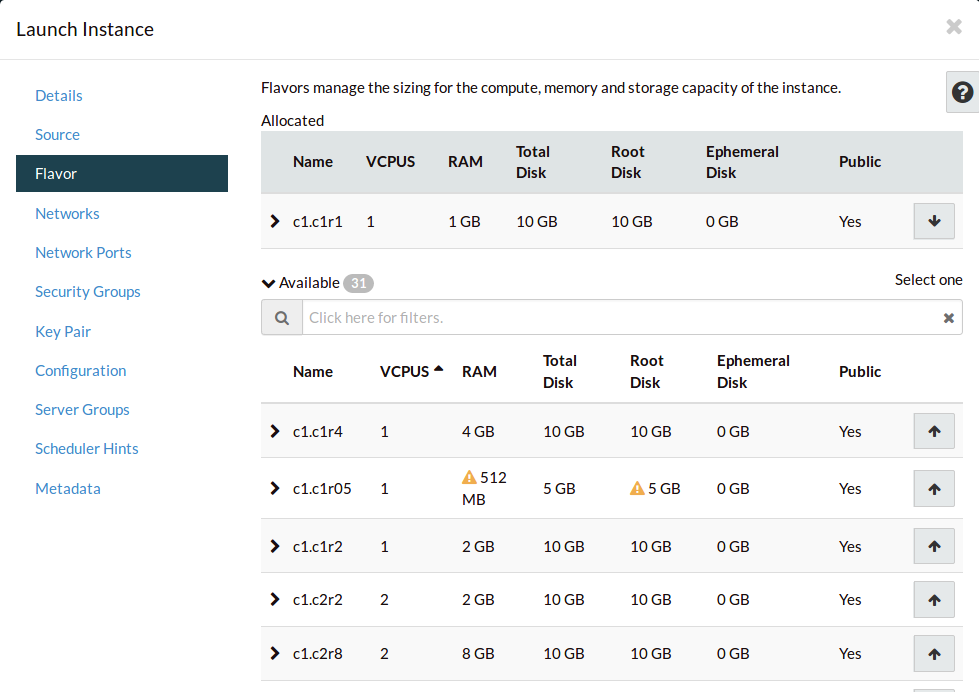
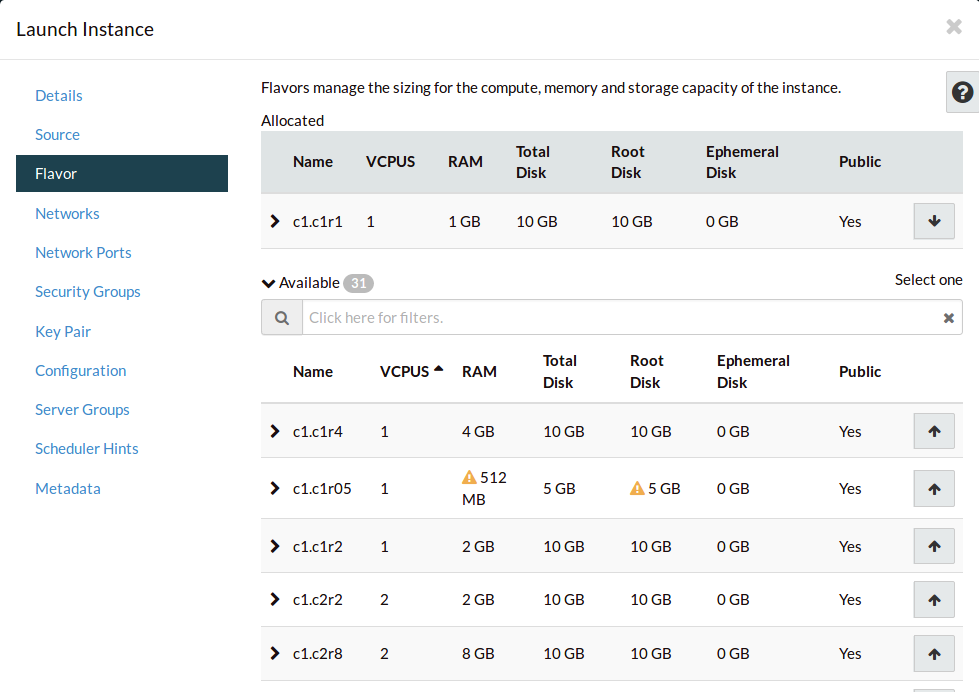
Navigate to the Flavor tab. This is where we select the compute resources
we want to assign to our compute instance. Flavors are described in more detail
in Instance Types.
Order the flavors by VCPUS, and select an appropriate size.
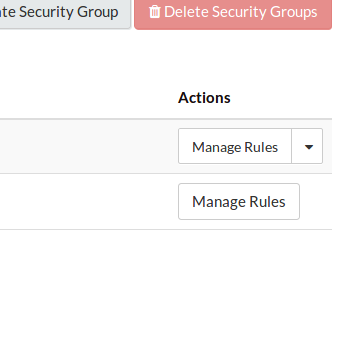
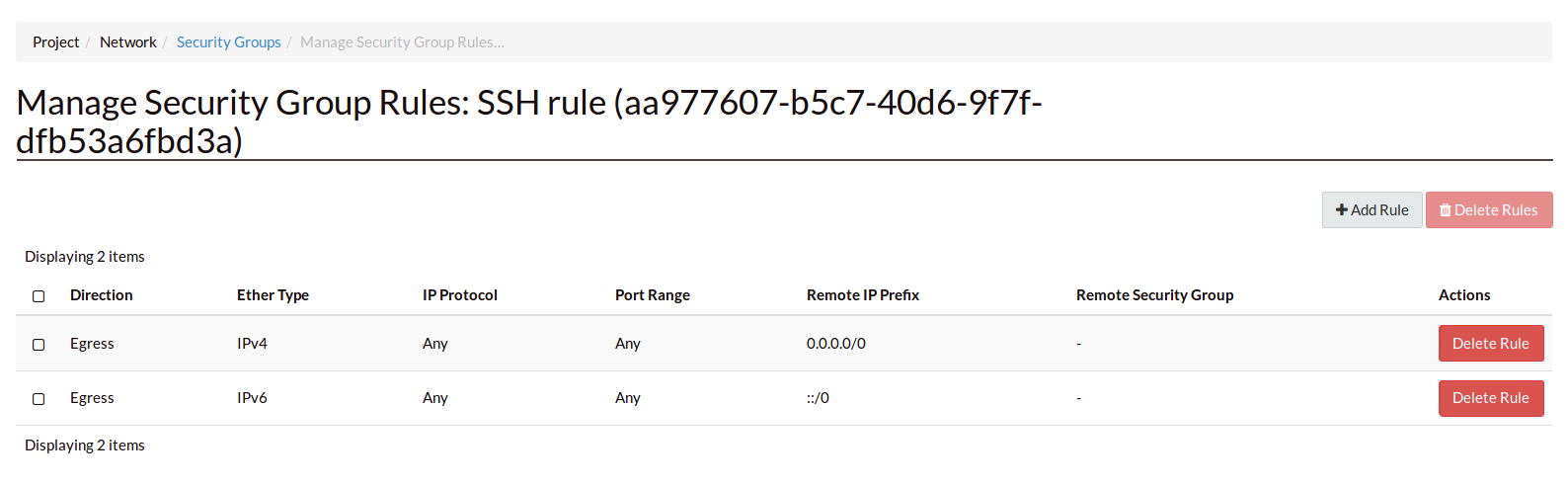
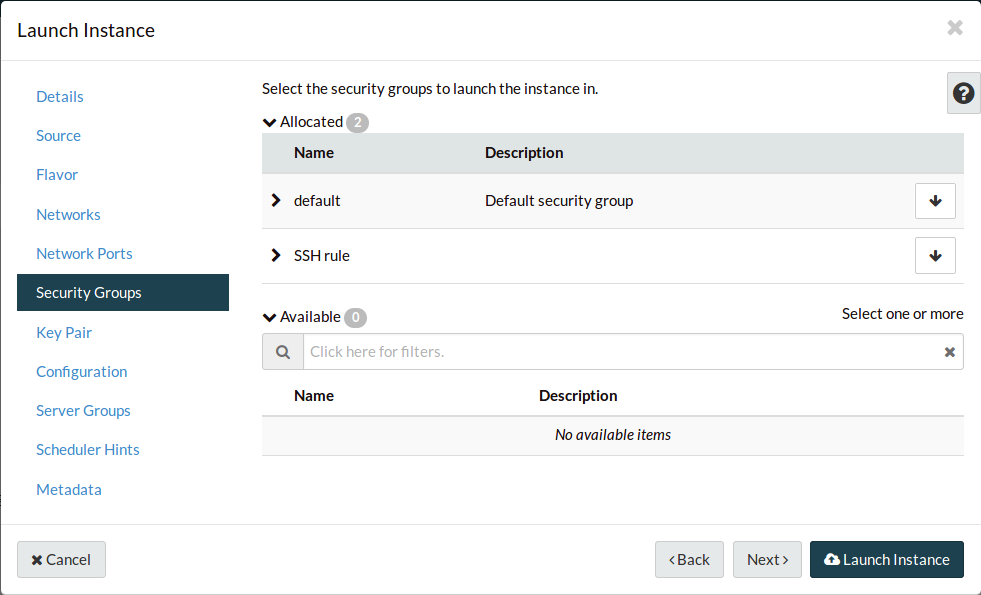
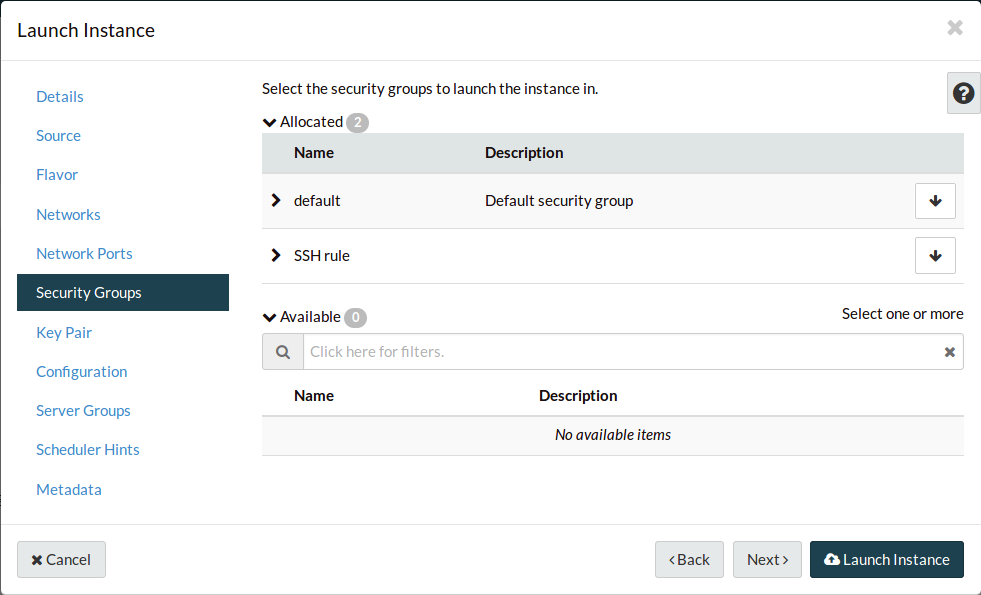
Navigate to the Security Groups tab. Add your new security group.
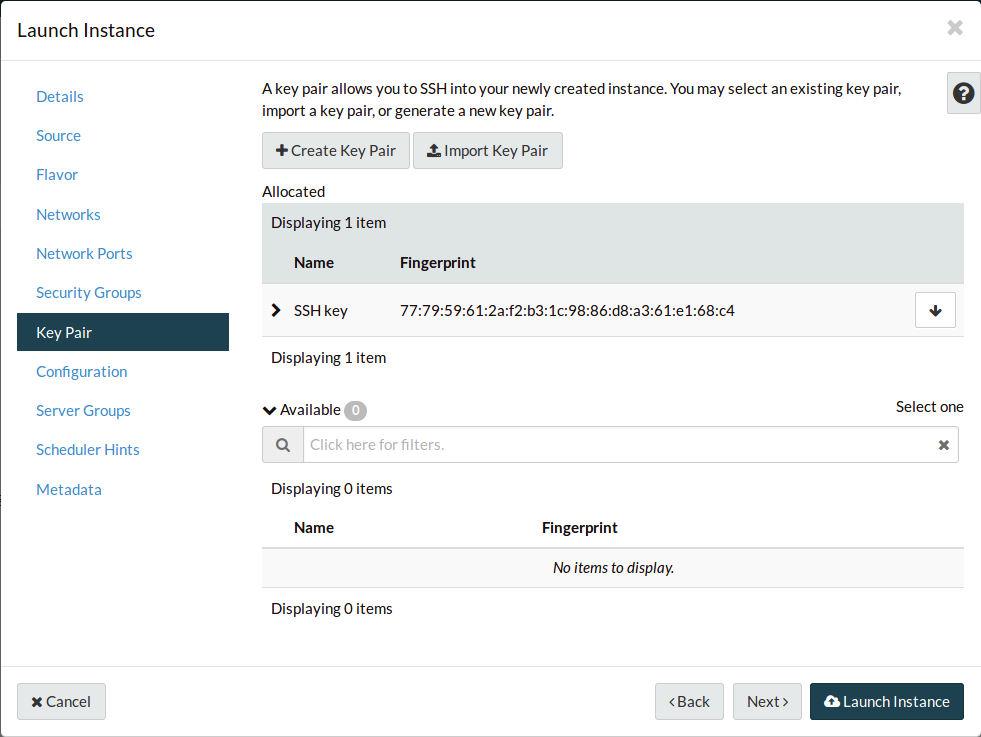
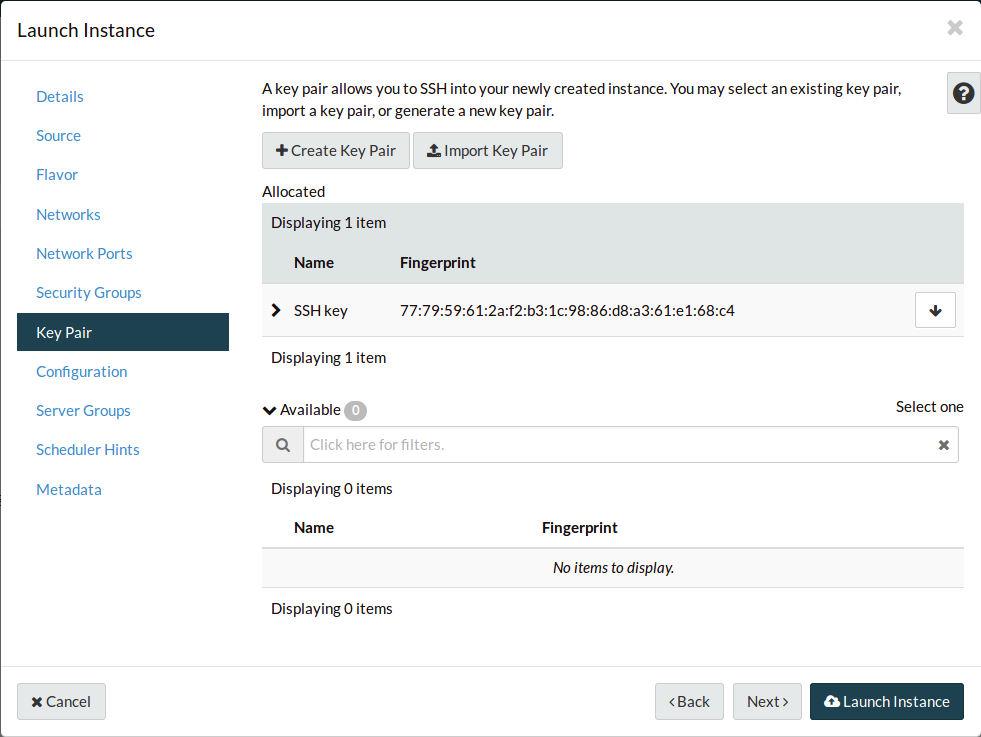
Navigate to the Key Pair tab. Your key pair should already be assigned, but
if it’s not, do it now. This will inject your public key into the new instance,
so that your private key will be accepted for SSH connections.
All the other tabs are for advanced features, and we can safely ignore them for
now.
Select Launch Instance.
Finally, to make your instance accessible, we need to give it a publicly
available, static IP address, because currently the instance only has an
internal IP address from instance’s subnet. These are Floating IPs.
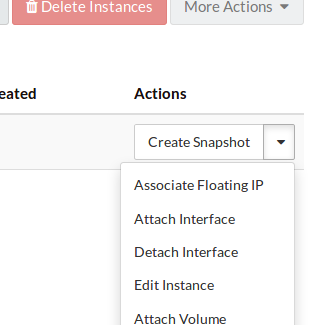
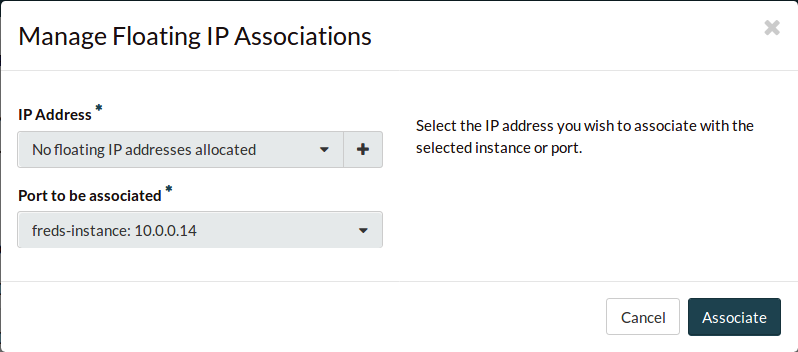
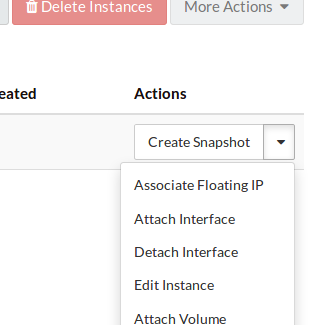
Use the instance’s dropdown to find the Associate Floating IP option and
select it.
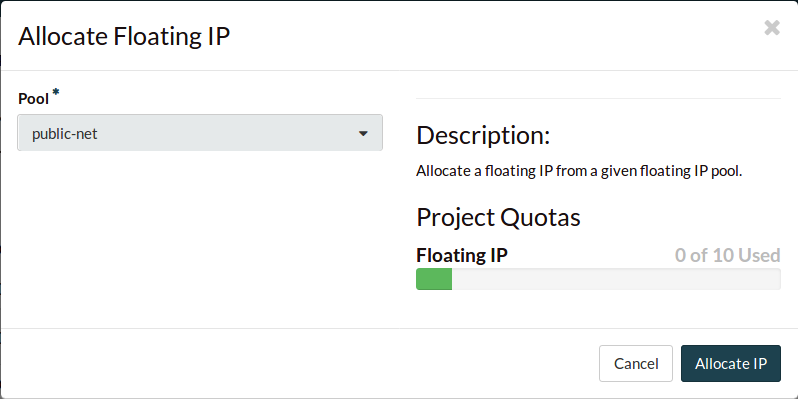
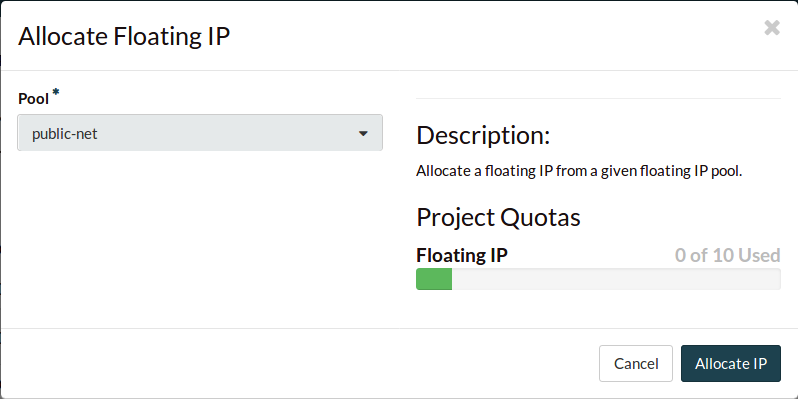
Select the + to create a new floating IP address.
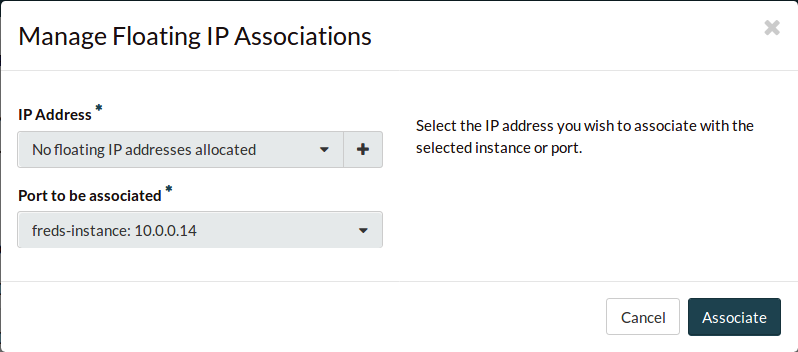
Select Allocate IP to provision yourself a floating IP address.
The new floating IP should already be assigned.
Select Associate to associate it to your instance.
Congratulations, you’ve now booted an instance. Now we’ll connect to it with an
SSH tunnel so you can start using it.
Connect to the new instance
Before we SSH in, we should give the private SSH key the correct, more secure
permissions.
$ chmod 600 <path to private key>
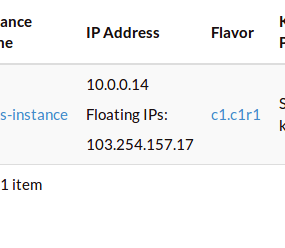
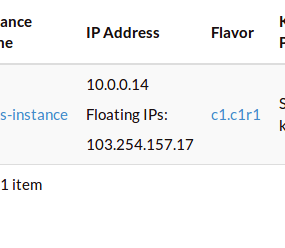
You can now connect to the SSH service using the floating IP that you
associated with your instance. This address is visible in
the Instances list, or under the Floating IPs window.
$ ssh -i <path to private key> ubuntu@<your floating ip>
You should be able to SSH into, and interact with this instance as you would
any Ubuntu server.